NAT (Network Address Translation) is an IPv4 tool that is not used in most IPv6 deployments. This has caused some users to ask whether IPv6 is as secure as IPv4.

What is NAT?
NAT is a tool that allows multiple computers behind an Internet connection to share the single address of that connection. Thus, if I have thirty computers in my office, they can all share a single connection. On the internet, all the traffic comes from the connection's address; inside the local network, each computer has a unique address on that LAN. The mechanism is simple to implement and is found in most routers, including home and small office routers.
NAT was never intended as a security feature, per se! Instead, it was designed and deployed to "address" the diminishing number of IPv4 addresses available. However, it does have some security value: the addresses of the individual computers on a network do not appear on the internet, so attackers cannot see them directly.
Why doesn't IPv6 use NAT?
IPv6 doesn't use NAT mainly because it doesn't need it! There are many more IPv6 addresses than IPv4 addresses (340,282,366,920,938,463,463,374,607,431,768,211,456 vs 4294967296, though not all in each group are usable!), and thus every device can have a unique one. There is a specification for NATv6, but it is seldom used.
One issue with not using NAT is that if a computer uses a consistent address over the internet, it can be tracked and potentially identified. Fortunately, there is a fix for that. The fix is to use a temporary address that changes every so often. In that way, observers on the internet cannot see and track a specific address. The first part of the temporary address will reflect the Internet provider and organization, and the last part will change. How big each of those parts is will depend on the organization's size. In my case, the last 64 bits of the address change.
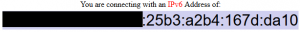
The Windows tool ipconfig shows the addresses a device uses. Here is part of the output from my desktop PC (with the prefix obscured):
IPv6 Address. . . . . . . . . . . :xxxxxxxxxxxxxxxxxxxx:791a:da6a:a3b8:5759Temporary IPv6 Address. . . . . . :xxxxxxxxxxxxxxxxxxxx:25b3:a2b4:167d:da10Link-local IPv6 Address . . . . . : fe80::791a:da6a:a3b8:5759%6
Note the temporary v6 address. The third line is my address on the local network. Here is what the site https://whatismyv6.com/ shows as my address:
So is a temporary address enough?
No. A temporary address provides some anonymity but will not protect your computer. To protect your computer, you need a filtering firewall (as in a corporate firewall or the firewall in your home router) and a personal firewall on your computer (whether the one in Windows or a third party such as Zonealarm). Please use both: this is called "defense in depth" and is a core of good physical or network security.
Using an online scanning tool, you can test whether the firewall is blocking ports. I have used http://www.ipv6scanner.com/cgi-bin/main.py, but I'm not endorsing it, per se.
So even though NAT is not generally a part of an IPv6 deployment, the available features provide the anonymity NAT did. Good practices such as a network and personal firewall continue to be necessary to protect local devices.
To your safe computing,
John
This piece was originally posted on Oct 12, 2021, and has been refreshed with updated styling.